In this article, you’ll learn the basics about a type of cybersecurity strategy that hackers despise and that has grown by 200% in just the last 2 years.
It’s called Managed Detection and Response Services (MDR), or “SOC-as-a-Service,” and it’s a hybrid security approach that takes the best of technologies, like AI and Machine Learning, and combines it with a team of security experts who work around the clock, 24/7.
Why has MDR become so popular?.
Well, in the past hackers were easy to stop with basic tools like passwords, firewalls and prevention tools like anti-virus.
But hackers are smart nerds who use automated strategies to keep trying until an opening is discovered. And what happens once they breach? They get what they want: access to a network, time to learn the ins and outs, and finally, they extract your assets without being detected.
MDR is an offensive strategy that reduces a hacker’s time once they’ve breached, and in this article, we’ll explain how it works and how you can decide if it’s right for you.
What is Managed Detection and Response?
Managed Detection and Response (MDR), also known as SOC-as-a-Service, is a layer of cybersecurity that includes threat hunting and response services by qualified cybersecurity professionals. What makes this layer different is the qualified human element; in an MDR model, security researchers and engineers analyze incidents and respond to cases they deem as legitimate threats.
If having excellent security training and firewalls is like having an iron fence and security guards outside your house from 9 to 5, then MDR represents a group of martial artists inside your house watching every window 24/7.
Today’s Cybersecurity Landscape and the importance of MDR
According to the 2019 Verizon Data Breach Investigation Report, 56% of breaches affecting SMBs took months or longer to discover. Threat detection and response clearly isn’t easy for companies of any size; the standard preventive security tools, such as antivirus, firewalls, and email protection, can’t help once a hacker finds a way around them.
The high likelihood of a breach is why security strategy should be discussed in terms of multiple “layers” or ”levels,”; we need to balance the layers of prevention, detection, and response to be fully prepared. It’s better explained using a house security analogy:
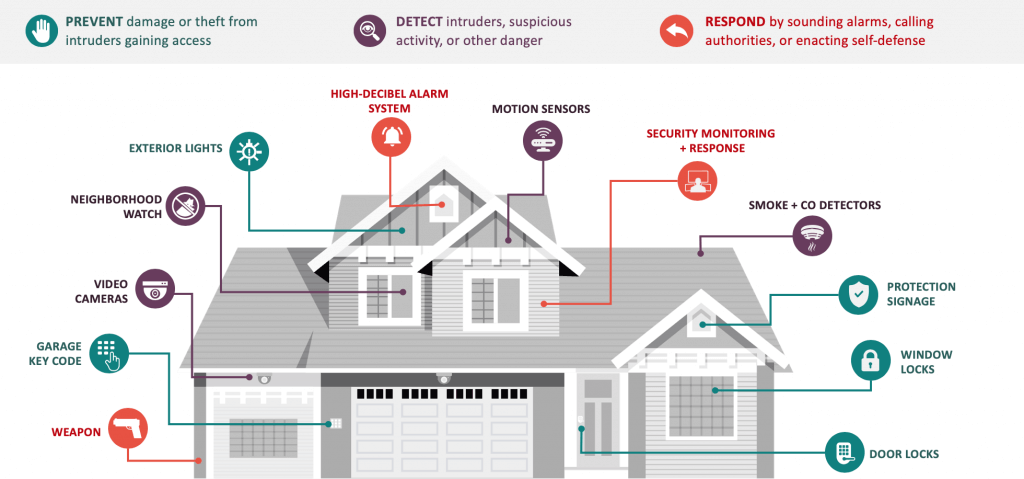
Big locks and complex garage key codes are tools to prevent a criminal from entering your house, but if they find an open window, what do you have in place to detect them, and how will you deal with them? That’s why getting video cameras and motion sensors that are supervised by security guards 24/7 is a smart idea.
Here’s the bottomline: if something sneaks by your end-point protection, you’ll need to detect and respond to the threat before they take your entire business down.
However, most organizations can’t deploy internal detection and response teams, in fact in 2019, ESG research showed that 27% of businesses admit their organization tried threat detection and response technologies but found them to be beyond their abilities, so they turned to “Managed” detection and response as an alternative. As explained before, there is a human element to an MDR Service, which is the expertise of those security engineers who prioritize every action. The network monitoring technologies in place will present data that only these engineers can assess and take action in a timely matter. In a nutshell, MDR becomes your last crucial layer of cybersecurity.
MDR vs. MSSP vs. IT
Be careful of making the right distinction between an MDR service, a Managed Security Service Provider (MSSP), and an IT team.
The differences can get technical so I’ll do my best with a football analogy.
A good football team can have a great player, like a superstar quarterback, but they never win championships because the talent of the quarterback isn’t enough against a smart team, especially if they know every weakness the quarterback has.
Companies with great IT teams are like the football team with a star quarterback. Unfortunately, a smart hacker can find the weaknesses in a network and exploit it without getting noticed by IT. For IT Teams, security responsibilities may fall on a systems engineer who, despite his or her best efforts, won’t have the time or security-specific experience to identify the hacker and handle him accordingly.
Now, with an MSSP, the issue of “lack of security expertise” seems to be resolved, it has the word security in there, right? The answer is “potentially, but not necessarily.” Here are some of the main differences between these MSSPs and MDR teams:
- The human element. MSSPs send automated reports on an ongoing basis that don’t necessarily have actionable data that’s easy to understand. However, with an MDR, in addition to the reports, you’d get direct communication with your designated security team; they truly become an extension of your IT department.
- Pricing for incident response. For an MSSP, the standard service mainly includes the monitoring and management of your security environment (detection), but incident response an additional price. But with an MDR, you’ll find an incident response team included with the service for no additional cost.
- Coverage and Compliance. While MSSPs can work with different types of event logs, the customer decides which security data to send to the MSSP, which may not give a full view of the network and thus result in compliance failure But for MDR services, they use their own event log tools and tailor them to your compliance needs.
Benefits of Managed Detection and Response
I’ve covered some of the main benefits of a Managed Detection and Response Service, but in case you missed it:
- MDR reduces breach damage by quickly detecting and responding to threats.
- MDR services are more affordable than building a security team and far less than the potential costs of recovering from a cyberattack.
- MDR services check the compliance and regulations box for your industry. It includes dashboards and reports necessary to make sure your firm is compliant.
- The success of MDR teams depends on their ability to see multiple networks at once. The insights captured in one network can be shared amongst the rest, strengthening the cybersecurity capabilities.
Things to consider when choosing an MDR Service
- Not all managed detection and response service providers offer the same services or technology. Be sure to choose wisely and select the one that is a perfect fit for your organization’s size, security controls, and needs.
- Make sure the MDR has processes in place to prioritize alerts, generate threat intelligence reports, and threat lifecycle visibility. The combination of these valuable insights will help you prioritize your future cybersecurity investments.
- Data and privacy regulations should be respected. Be sure that you choose a provider that is able to meet the compliance requirements you need to observe.
There you have it, everything you need to know about MDR Services. Ultimately you need to make sure the Managed Detection and Response service you hire offers you: false alarm filtering, threat intelligence reports, and threat lifecycle visibility. This will provide a 360-degree view of your security environment, creating an incident response plan that works for your business.
Next week we’ll share our MDR Buyer’s Guide with all the info you need to know to evaluate a Managed Detection and Response Provider. Stay tuned!
